20 November 2020. BBC: Dutch police have questioned a security researcher who said he successfully logged into the US president’s Twitter account by guessing his password.
Last month, well-known cyber investigator Victor Gevers said he had gained access to Donald Trump’s Twitter account with the password ‘MAGA2020!’.
The White House denied it had happened and Twitter said it had no evidence of a hack.
But Mr Gevers has now revealed more information to back up his claims.
As part of the police interrogation, Mr Gevers revealed for the first time that he had substantially more evidence of the “hack” than he had previously released.
He did not reveal exactly what information he had, but by logging in to somebody’s Twitter account someone would in theory be able to:
- see and send private messages
- see tweets that the user had privately bookmarked
- access information such as how many people the account holder had blocked
They would even be able to download an archive of all the user’s data, including photos and messages.
A spokesman for the Dutch Public Prosecution Service confirmed to De Volkskrant newspaper: “We are currently investigating whether something criminal has happened.”
The spokesman said their inquiry was an “independent Dutch investigation” and not based on a US request for legal assistance.
The police told the BBC that Mr Gevers had been questioned as a witness by the High Tech Crime Team and was not a suspect yet.
Police must first prove that the hack happened. If prosecutors consider Mr Gevers’ actions to be illegal and outside the realm of cyber-security research, he could face up to four years in prison.
Mr Gevers told reporters of his hack on 22 October. Dutch news outlet Vrij Nederland first reported the story.
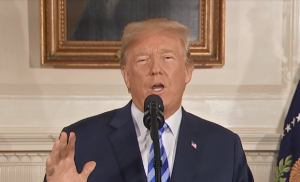
Donald Trump’s Twitter account has about 89 million followers.
Screenshots
Mr Gevers says he was doing a semi-regular sweep of the Twitter accounts of high-profile US election candidates on 16 October when he guessed President Trump’s password.
He did not post any tweets or change any settings, but said he took screenshots of some parts of the president’s account.
He said he had spent days trying to contact the Trump campaign to warn them about their security, which was lacking extra safeguards like two-factor authentication, before going to the press.
Two-factor authentication is a widely-used security system that links a phone app or number to an account, to add an extra step to the process of logging in.
The US president’s account is now secure.
Scepticism
At the time, Twitter said: “We’ve seen no evidence to corroborate this claim. We proactively implemented account security measures for a designated group of high-profile, election-related Twitter accounts in the United States, including federal branches of government.”
Twitter refused to answer any further questions about the hack, including whether or not the extra security measures were permanently enforced or if the company even has access to the president’s account activity.
Mr Gevers’ story has been met with scepticism by some in the information security world as his screenshots could have been faked.
However, he claims to have a lot more data. He hopes he will not have to disclose it to prosecutors but says he is prepared to if necessary.
He said: “I have evidence that was not included in the responsible disclosure to the Trump team because it did not add anything in alerting the victim of the risk.
“I have shown some of it to a select group of journalists. Police asked me if I was willing to show it and I said no. Only if there is an indication of wrongdoing will the archived material be unlocked.”
The BBC has seen some evidence but has not been able to verify whether all the additional material is genuine.
But Mr Gevers says he is standing by his account of events and hopes that his actions are ruled to have been a normal part of his job as an ethical hacker.
“There should not be a reason for the Dutch National Police, especially the team at the High Tech Crime Unit, to doubt my statement. They know me, they know my work for more than 22 years with the Dutch Institute for Vulnerability Disclosure.
“I did not ‘hack’ Trump’s account, I did not bypass any security system as there was no adequate security in place. I just guessed the password and then tried to warn his team about the risks and how to solve them.”
Earlier this year, Mr Gevers also claimed to have successfully logged into Mr Trump’s Twitter account in 2016.
In that login he and other security researchers used a password linked to another of Donald Trump’s social network accounts that was discovered in a previous data breach.
In that instance Mr Gevers claims the password was another famous catchphrase from the reality TV star and politician: “yourefired”.